What Is WebVerse Labs? (And How It’s Different From PortSwigger, Hack The Box, and TryHackMe)

If you’ve searched for WebVerse, WebVerse Labs, or “what is WebVerse?”, this page is the clear answer.
WebVerse Labs is a hands-on web and API security lab platform focused on realistic exploit chains, modern web application behavior, and practical offensive security learning. It is built for people who want to practice the kinds of vulnerabilities and attack paths found in real web apps and APIs — not just isolated toy examples.
At a high level, WebVerse gives you:
- Web hacking labs
- API security labs
- Learning tracks for specific vulnerabilities (e.g., SSRF, authorization failures)
- Lab tracks with full multi-step challenges
- Walkthrough content and writeups to help you learn how real exploit chains work
If you’re coming from platforms like PortSwigger Web Security Academy, Hack The Box, or TryHackMe, the simplest summary is:
- PortSwigger is excellent for structured vulnerability-focused web exercises
- Hack The Box is broader and often machine/network/pentest oriented
- TryHackMe is beginner-friendly with guided learning rooms and paths
- WebVerse Labs focuses heavily on web + API attack chains, realistic multi-surface applications, and practical vulnerability chaining in a way that feels closer to modern app environments
What Is WebVerse?
WebVerse is a platform for practicing web application and API exploitation through intentionally vulnerable labs.
The goal is not just to show one bug in isolation, but to help you learn how vulnerabilities often chain together in real applications, such as:
- information disclosure → authorization bypass
- GraphQL enumeration → sensitive field exposure → account takeover
- privileged dashboard access → SSRF → internal pivoting
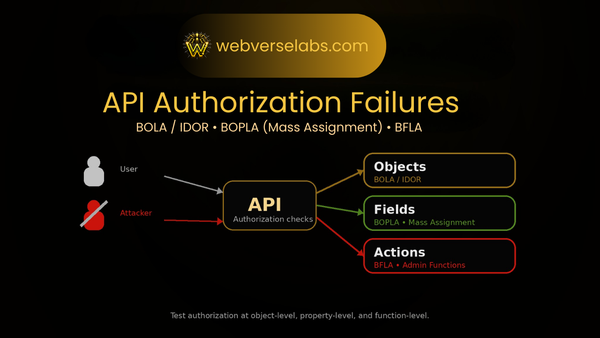
- API authorization flaws (BOLA/BOPLA/BFLA) → privilege escalation or data exposure
WebVerse is designed for people who want to build skill in areas like:
- Web application penetration testing
- API security testing
- Bug bounty-style recon and chaining
- Realistic multi-step exploitation workflows
- Modern attack surface mapping (subdomains, APIs, internal tooling)
What Is WebVerse Labs?
“WebVerse Labs” refers to the hands-on lab content and learning environment within WebVerse.
When people search “WebVerse Labs,” they’re usually looking for one of these:
- What the platform is
- What kinds of labs it has
- Whether it focuses on web/API hacking
- How difficult the labs are
- How it compares to other training platforms
- Whether it has walkthroughs or learning tracks
The short answer:
WebVerse Labs is a web and API security lab ecosystem built around realistic, intentionally vulnerable applications and guided learning content.
It includes both:
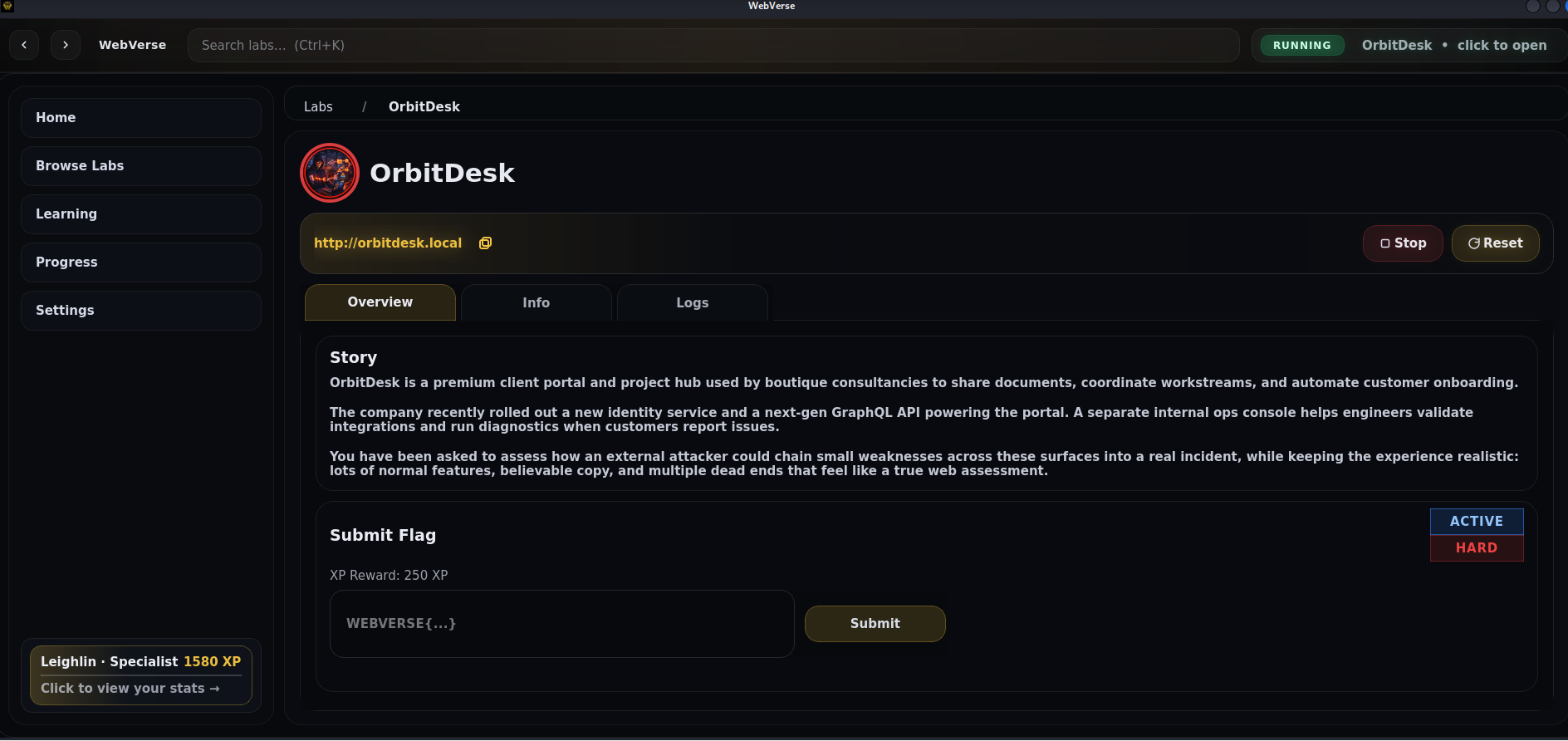
1) Lab Tracks (full labs)
These are more complete challenge environments where you need to perform recon, map the attack surface, find vulnerabilities, and chain them into a successful compromise.
Think:
- multiple subdomains
- separate services
- API endpoints
- auth flows
- dashboards/internal tooling
- flags/objectives
2) Learning Tracks (concept-focused mini labs)
These are focused, smaller challenges designed to teach a specific concept or vulnerability pattern more directly (for example: SSRF basics, filter bypasses, GraphQL enumeration, authorization failures).
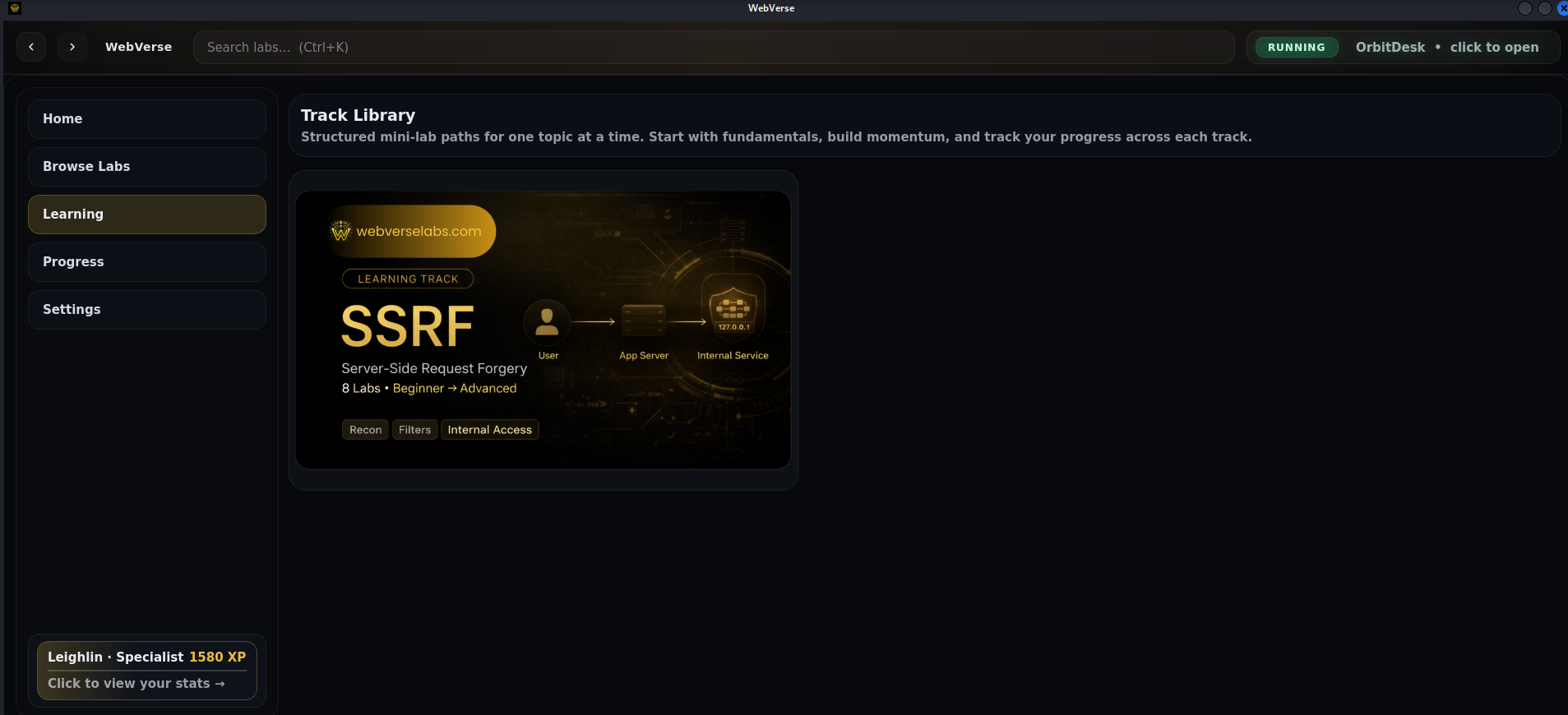
This distinction matters because it lets learners choose between:
- “Teach me the concept” (Learning Track)
- “Make me apply it in a realistic app” (Lab Track)
How Many Labs Does WebVerse Have?
This is one of the most common brand searches, and it’s a great question.
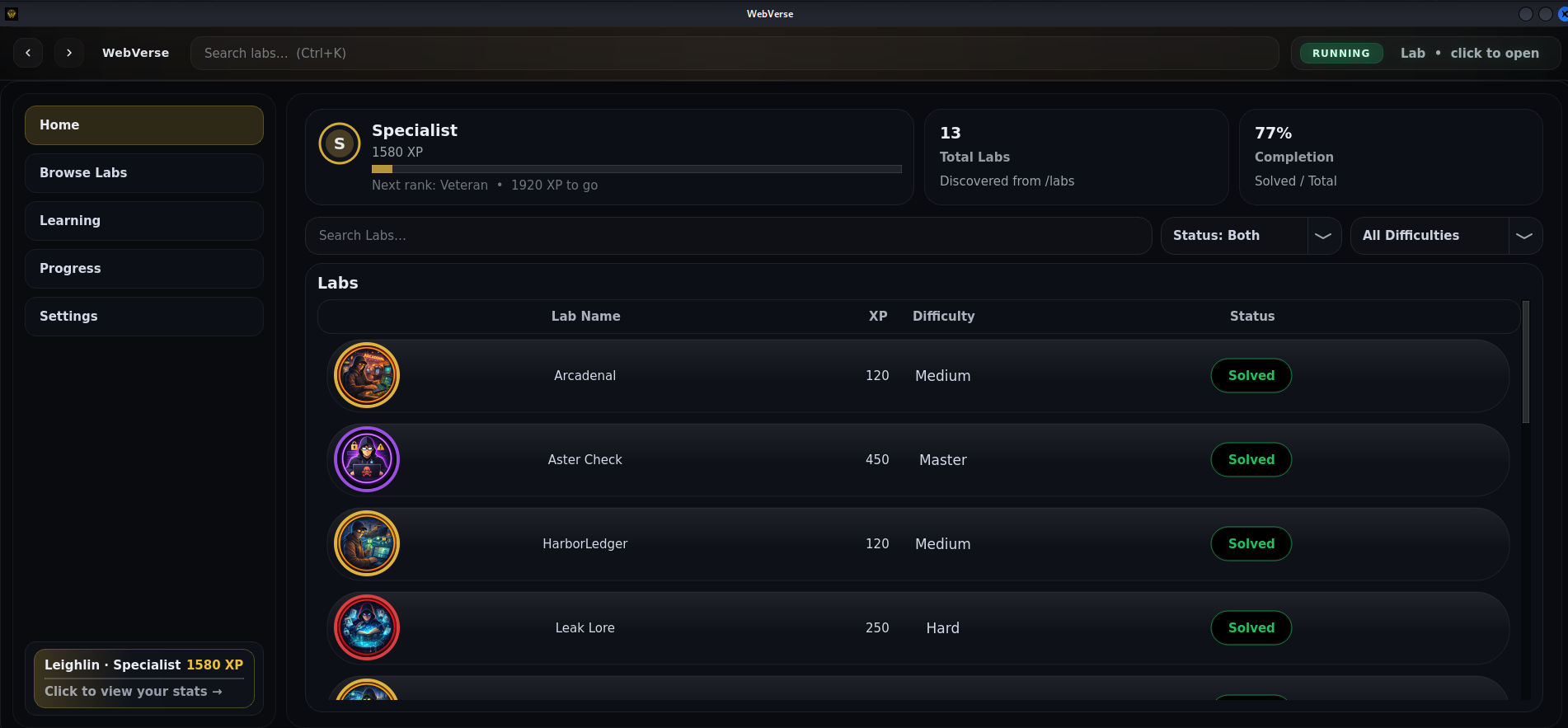
As of February 2026, WebVerse has 13 labs, with additional labs and learning-track content being added every week.
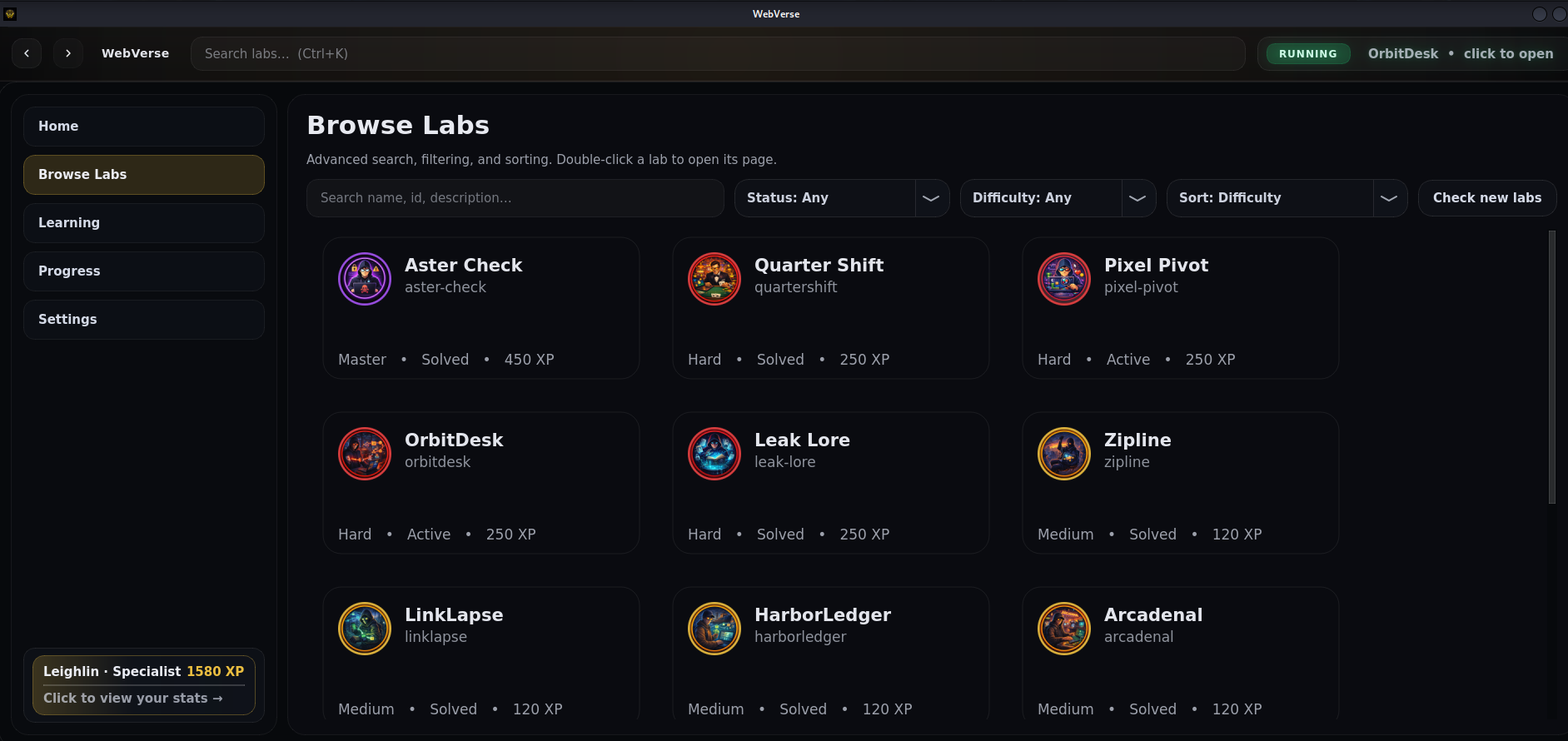
What Kind of Labs Are in WebVerse?
WebVerse is centered around web and API security, so the content tends to focus on vulnerabilities and attack paths you’d encounter in modern applications.
Common themes include:
- API authorization failures (BOLA / IDOR, BOPLA / mass assignment, BFLA)
- SSRF (including internal pivoting)
- GraphQL security issues (introspection abuse, sensitive field exposure, weak auth logic)
- Information disclosure (source maps, debug data, leaked headers, exposed configs)
- Authentication / reset flow abuse
- Privilege escalation through application logic
- Multi-subdomain recon and attack surface mapping
This makes WebVerse especially useful for people who want practice that mirrors how real web/API assessments often unfold:
- Recon and mapping
- Behavioral testing
- Vulnerability validation
- Chaining and pivoting
- End-to-end impact
How Is WebVerse Different From PortSwigger?
This is another search people will make, especially if they already know PortSwigger Web Security Academy.
PortSwigger is excellent and highly respected for learning web vulnerabilities in a structured way. WebVerse is not trying to replace that. It is trying to offer something different in emphasis and experience.
WebVerse vs PortSwigger (high-level)
- PortSwigger: extremely strong vulnerability-focused training and methodology, especially for classic and advanced web security topics
- WebVerse: focused on realistic web/API exploit chaining, modern app flows, and multi-surface labs that feel like full applications rather than isolated exercises

In practical terms, WebVerse emphasizes:
- realistic app behavior and flows
- chaining multiple weaknesses together
- subdomains, APIs, dashboards, internal tools
- scenario-driven objectives
- concept-specific learning tracks + full labs
If you want to learn what a bug is, PortSwigger is incredible.
If you want to practice how bugs chain inside realistic web/API apps, WebVerse is built specifically for that.
WebVerse vs Hack The Box vs TryHackMe vs PortSwigger
People compare these because they serve overlapping audiences — but they’re not the same type of platform.
PortSwigger Web Security Academy
Best known for:
- structured web vulnerability education
- high-quality explanations
- focused labs for specific bug classes
Hack The Box
Best known for:
- machines, networks, and broader offensive security training
- pentesting workflows across many domains
- a strong challenge and certification ecosystem
TryHackMe
Best known for:
- guided beginner-to-intermediate learning paths
- approachable rooms
- step-by-step teaching style
WebVerse Labs
Best known for:
- web + API-specific labs
- realistic attack chains
- modern app-style multi-surface targets
- learning tracks for focused practice + lab tracks for full challenge experience
The goal isn’t “pick only one.”
A lot of learners use multiple platforms. WebVerse is built to be the one you reach for when you want to get stronger at:
- web app recon
- API testing
- exploit chaining
- realistic application behavior
Who Is WebVerse For?
WebVerse is a strong fit for:
- Web app pentesters
- API security testers
- Bug bounty hunters
- Students learning offensive web security
- Red teamers who want more web/API chaining practice
- Security engineers who want hands-on practice instead of just reading theory
It’s especially useful if you feel like you’ve learned vulnerability names, but want more reps on:
- “How do I actually find this in a real app?”
- “What does the attack path look like end-to-end?”
- “What does this unlock?”
- “How do I pivot from one bug into another?”
Why WebVerse Exists
A lot of security learners hit the same problem:
They can identify a vulnerability category in theory, but struggle when they need to apply it inside a realistic app with multiple routes, subdomains, auth flows, and hidden assumptions.
WebVerse exists to close that gap.
It focuses on teaching how to think through real application behavior:
- What is this endpoint doing?
- What trusts what?
- What data should be hidden?
- What happens if I modify this header/body/ID?
- What does this unlock next?
That’s the mindset that turns isolated bug knowledge into practical offensive skill.
Examples of What You Can Practice on WebVerse
Some WebVerse labs are designed around multi-step chains like:
- subdomain discovery → GraphQL introspection → sensitive field exposure → account takeover → SSRF pivot
- API authorization failure → privilege escalation → admin function access
- source map disclosure → hidden client logic → access tier abuse
- internal tooling abuse through trusted features (exports/imports/fetchers)
These aren’t just “click a button and get a flag” labs — they’re built to train the habit of:
- mapping the attack surface
- testing assumptions
- chaining behavior
- proving impact
How to Get Started With WebVerse
If you’re new to WebVerse, a good starting approach is:
- Start with a learning track (concept-focused)
- Solve a few mini challenges on one vulnerability class (e.g., SSRF or API auth)
- Move into a full lab track
- Use walkthroughs/writeups after your attempt to understand the chain deeply
- Repeat with a different vulnerability family
This helps you build both:
- concept mastery
- application-level problem solving
FAQ: WebVerse Labs
What is WebVerse?
WebVerse is a web and API security training platform focused on hands-on labs, realistic exploit chains, and practical offensive security learning.
What is WebVerse Labs?
WebVerse Labs is the lab ecosystem inside WebVerse, including full labs (lab tracks) and concept-focused mini challenges (learning tracks) for web and API security practice.
What kind of vulnerabilities can I practice on WebVerse?
WebVerse focuses on real-world web and API issues such as SSRF, API authorization failures (BOLA/BOPLA/BFLA), GraphQL security issues, information disclosure, auth/reset flow abuse, and exploit chaining.
How many labs does WebVerse have?
As of February 2026, WebVerse has 13 labs. This number changes as new labs and learning-track challenges are added every week.
Is WebVerse the same as PortSwigger Web Security Academy?
No. They overlap in audience, but they are different in focus. PortSwigger is excellent for structured web vulnerability education, while WebVerse emphasizes realistic web/API exploit chains and modern multi-surface application behavior.
How is WebVerse different from PortSwigger?
WebVerse is designed around realistic web and API attack chains, learning tracks + lab tracks, and scenario-driven practice that mirrors how modern applications behave (subdomains, APIs, dashboards, internal tools).
How is WebVerse different from Hack The Box?
Hack The Box is broader across offensive security domains (machines, networks, etc.). WebVerse is more specialized around web application and API exploitation practice.
How is WebVerse different from TryHackMe?
TryHackMe is very strong for guided, beginner-friendly learning paths across many topics. WebVerse is more specialized in web/API attack surface mapping and exploit chaining in realistic app-style labs.
Is WebVerse good for learning API security?
Yes — WebVerse is built with a strong emphasis on API security testing, including authorization failures, GraphQL security, chaining, and modern API-driven application behavior.
Who should use WebVerse Labs?
Web app pentesters, bug bounty hunters, API security testers, students, red teamers, and security engineers who want more realistic web/API hands-on practice.