API Authorization Failures: BOLA (IDOR), BOPLA (Mass Assignment), and BFLA
If you’ve ever seen an API return someone else’s data just because you changed an ID, you’ve run into one of the most common real-world web security problems: broken authorization.
API authorization failures usually don’t look like “a huge hack.” They look like a normal request that should say “no”… quietly saying “sure”.
This post is a practical guide to the most important authorization bug categories in modern web apps and APIs:
- BOLA / IDOR (Broken Object Level Authorization / Insecure Direct Object References)
- BOPLA / Mass Assignment (Broken Object Property Level Authorization)
- BFLA (Broken Function Level Authorization)
You’ll learn what each one is, how to spot them quickly, how to test them properly, and how developers should fix them.
Why API authorization bugs are everywhere
Modern applications are rarely “one app.” They’re multiple services, subdomains, APIs, dashboards, and internal tools — all stitched together.
That creates two big problems:
- The UI is not the security boundary.
If the backend trusts what the frontend hides, you get authorization failures. - Authorization gets duplicated.
One endpoint has checks, another endpoint forgets them, a third checks the wrong thing. Attackers only need one weak link.
Authorization failures are also easy to accidentally introduce because they’re logic bugs, not syntax bugs. Your code can be “working perfectly”… and still be insecure.
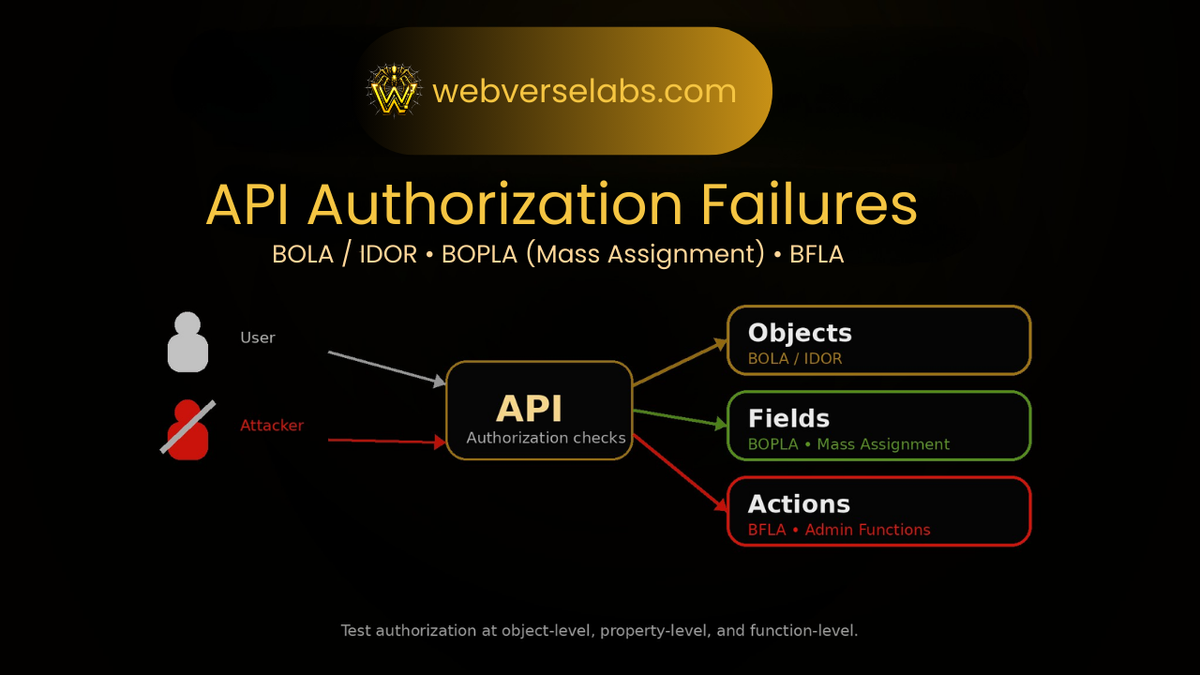
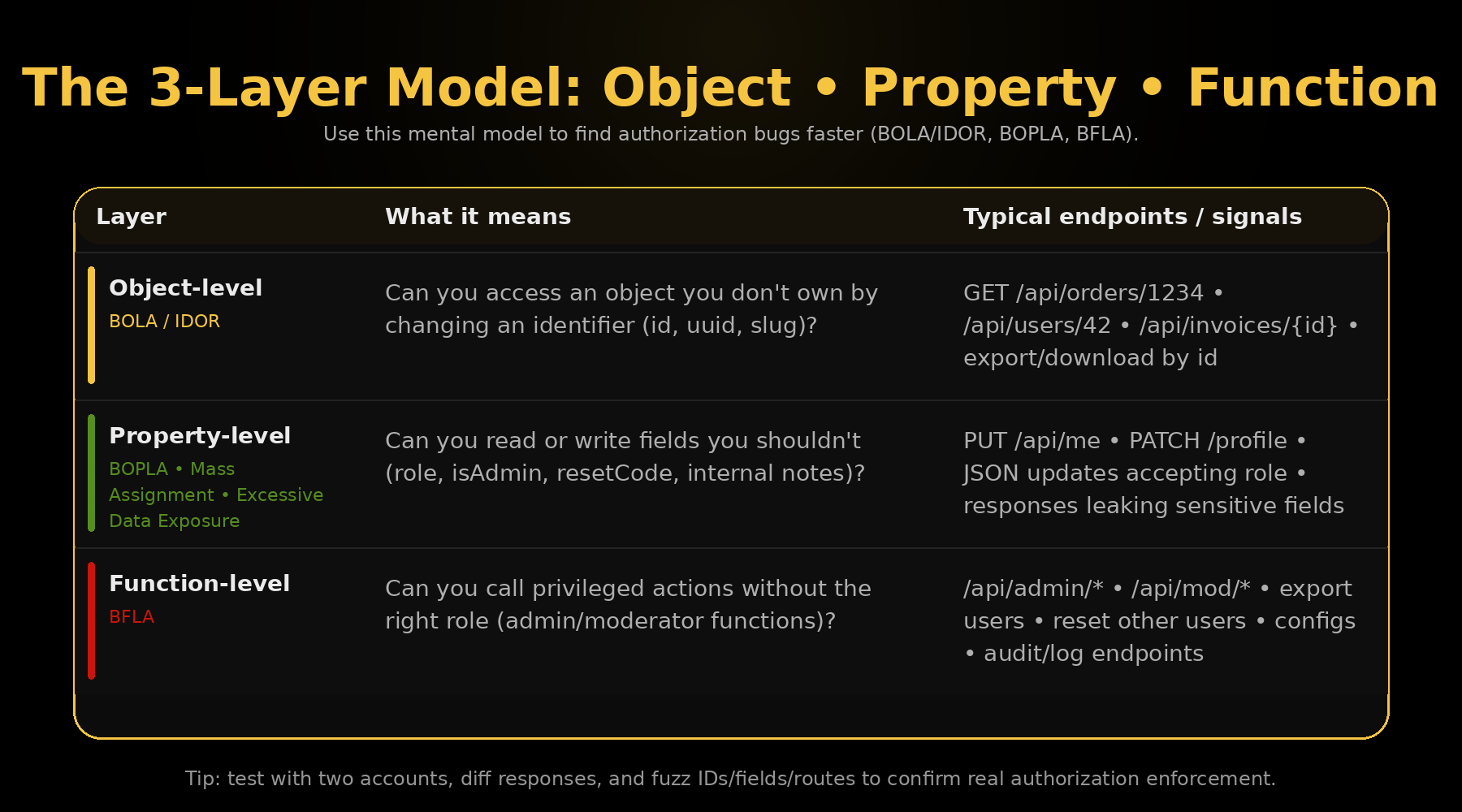
The 3-layer model: Object, Property, Function
When you’re testing an API, it helps to think in three layers. Almost every authorization bug fits into one of these:
1) Object-level authorization (BOLA / IDOR)
Can I access an object I don’t own?
Example: GET /api/orders/1234 returns another user’s order.
2) Property-level authorization (BOPLA / Mass Assignment / Excessive Data Exposure)
Can I read or modify fields I shouldn’t?
Example: update profile JSON accepts role: "admin" or response leaks resetCode.
3) Function-level authorization (BFLA)
Can I call an action I’m not allowed to perform?
Example: normal users can hit /api/admin/exportUsers.
BOLA / IDOR: Broken Object Level Authorization
What it is (plain English)
BOLA (Broken Object Level Authorization) is when an API uses an object identifier (ID, UUID, slug, etc.) but fails to enforce that the current user is allowed to access that object.
This is also commonly called IDOR (Insecure Direct Object Reference) — especially when the ID is directly used in the request.
What it looks like
These bugs show up anywhere you see object IDs:
- Path IDs:
GET /api/v1/invoices/9812 - Query IDs:
GET /api/v1/invoices?id=9812 - Body IDs:
POST /api/v1/export { "invoiceId": 9812 } - Nested IDs:
GET /api/v1/orgs/10/projects/44
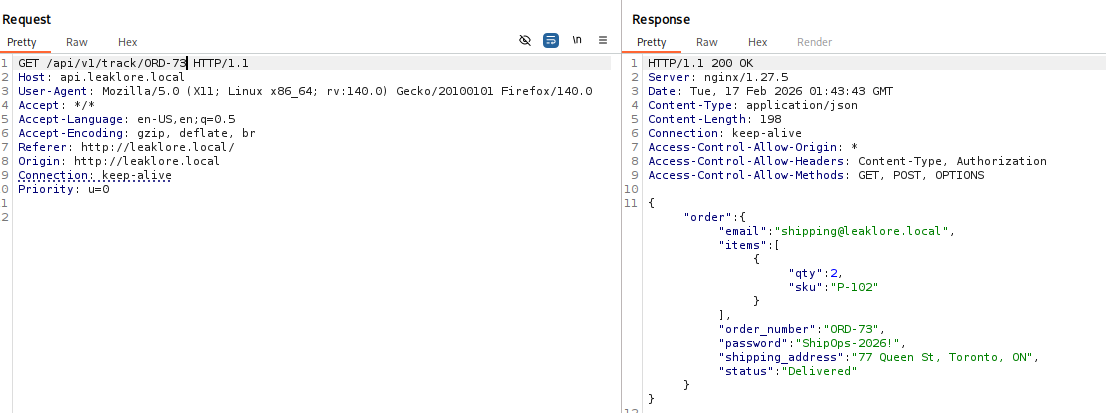
How to test BOLA/IDOR quickly (high-signal workflow)
- Create two accounts (or two roles) to compare access.
- Collect IDs by browsing normally:
- Network tab in DevTools
- API responses that list objects
- URLs inside JSON payloads
- Swap one ID at a time:
- Does it return 200?
- Does it return a different object?
- Does it return more data than expected?
- Diff the responses (this is huge):
- Status code (200 vs 403/404)
- Object owner fields
- Record counts
- Content length / structure
Why “I used UUIDs” doesn’t fix it
Developers sometimes think random UUIDs prevent IDOR. They don’t.
If a user ever learns or receives another object’s UUID (logs, emails, shares, UI leaks), authorization must still block it. UUIDs reduce guessing — they do not replace authorization.
Common BOLA hotspots (where to look first)
- Export / download endpoints (reports, invoices, receipts, PDFs, ZIPs)
- “View” endpoints for:
- tickets, incidents, cases, projects
- Anything with
?id=or/1234 - Multi-tenant endpoints with
orgId,teamId,tenantId
BOPLA: Broken Object Property Level Authorization
BOPLA is about fields, not objects.
There are two flavors, and both matter:
- Mass assignment (write): you can update fields you shouldn’t
- Excessive data exposure (read): you can view fields you shouldn’t
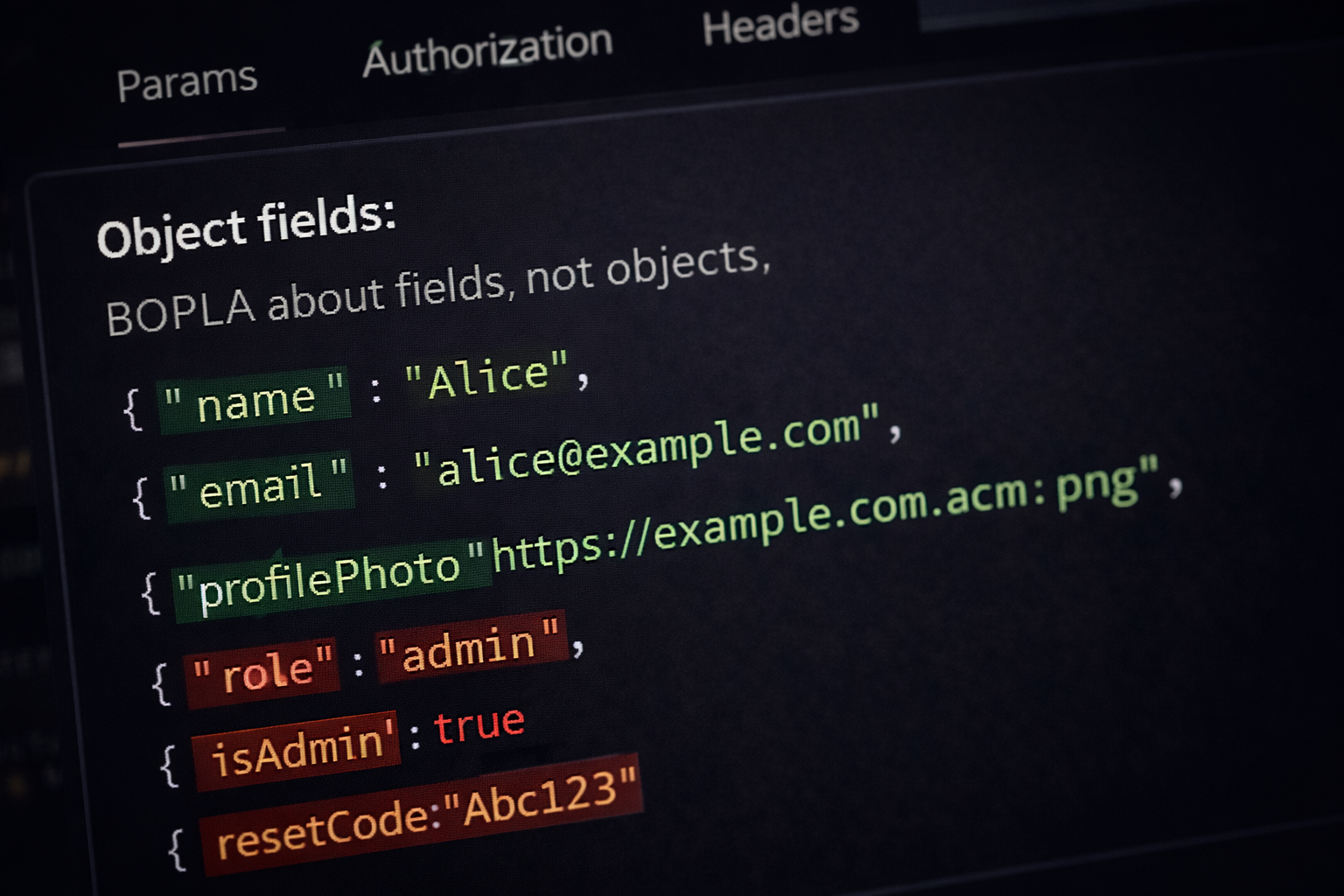
BOPLA (Write): Mass Assignment
What it is
Mass assignment happens when the backend takes client-supplied JSON and applies it too broadly — updating fields it should never trust the client to set.
Classic example:
- UI lets you update name/email
- API accepts
{ "name": "...", "email": "...", "role": "admin" } - Backend updates role because it doesn’t whitelist allowed fields
Where it shows up
PUT /api/mePATCH /api/profilePOST /api/account/update- “Settings” pages
- onboarding flows
- billing/plan endpoints
How to test mass assignment
- Intercept a normal profile update request
- Add high-signal fields:
role,isAdmin,permissionsplan,subscription,tieremailVerified,mfaEnableduserId,orgId(if present)
- Replay and check if:
- response includes the new value
- subsequent privileged routes become accessible
- token/session behavior changes (sometimes you need to re-login)
Why this is so common
Because developers love convenience patterns like:
- “update user from JSON”
- ORM update with client payload
Object.assign(user, body)- generic update endpoints
Those patterns are fast to build… and extremely easy to ship insecurely.
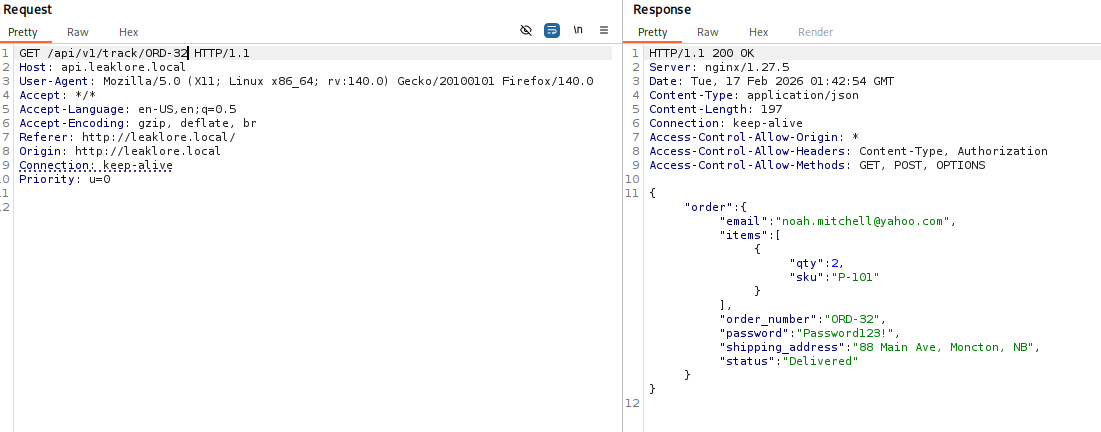
BOPLA (Read): Excessive Data Exposure
What it is
Even if you can’t modify forbidden fields, you might be able to see them.
That includes:
- internal notes
- staff-only fields
- reset tokens / reset codes
- hidden flags
- payment metadata
- role or permission structures
How to test it
- Compare the response for two users
- Look for fields that should be:
- omitted
- masked
- server-only
- Watch for “debug” fields or accidental serialization of full models
A great rule: if the frontend isn’t using a field, question why it’s being returned at all.
BFLA: Broken Function Level Authorization
What it is
BFLA is when an API exposes functions that should only be allowed for higher-privilege users (admin/moderator/staff), but the server doesn’t enforce that properly.
This often happens because:
- the UI hides admin buttons
- the endpoint still exists
- the backend doesn’t check role on the function route
What it looks like
/api/admin/*/api/mod/*/api/internal/*/api/v1/users/export- actions like:
- delete user
- reset password
- grant role
- view audit logs
- download full datasets
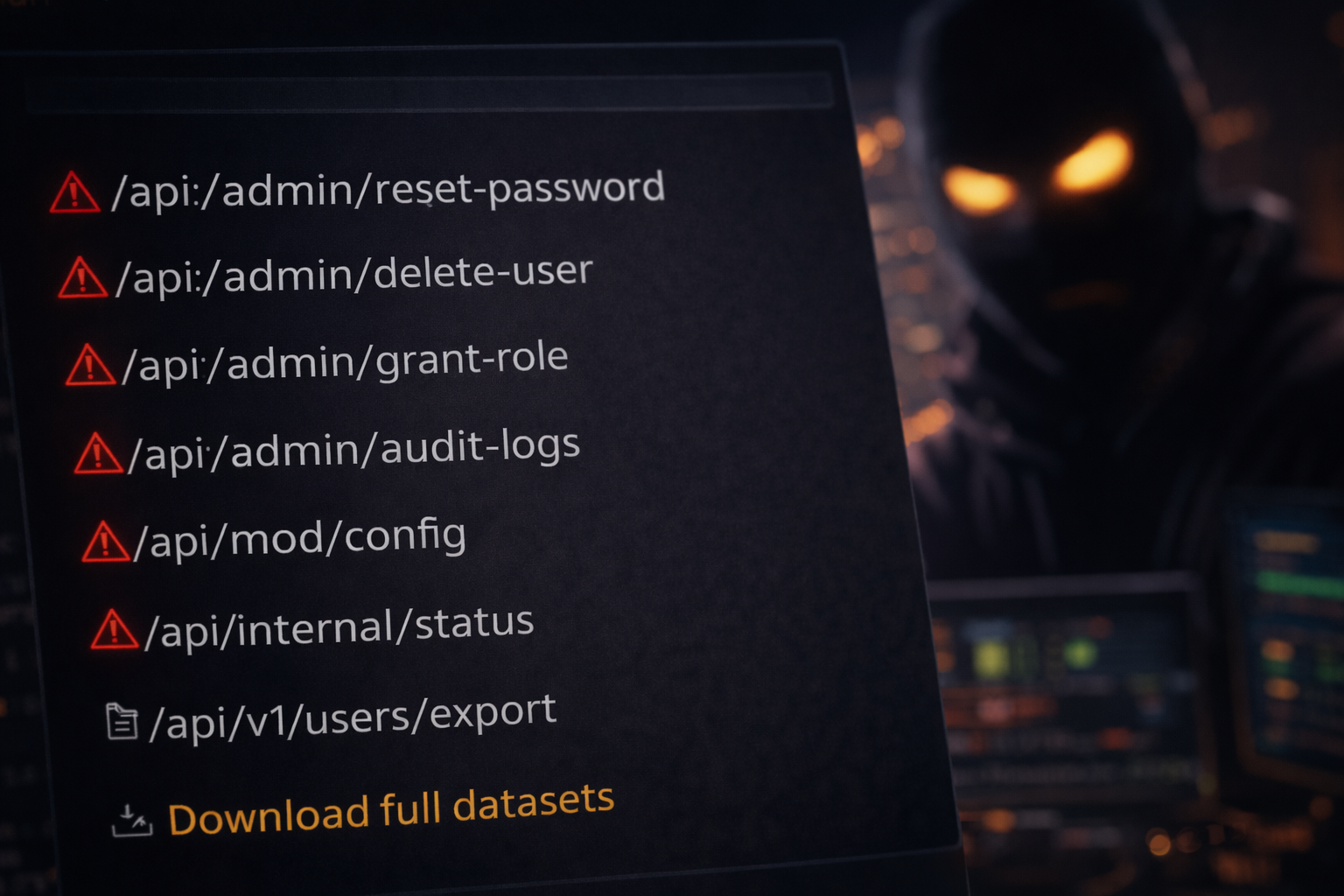
How to test BFLA
- Identify likely privileged functions:
- “export”
- “audit”
- “config”
- “moderation”
- Try them as a normal user:
- direct request
- replay from Burp
- Check response behavior:
- Are you blocked with 403?
- Are you redirected but still receive data?
- Is it “security by obscurity” (404) but actually accessible?
The practical testing playbook (copy/paste checklist)
When you’re hunting API authorization bugs, you want a workflow you can run on any target:
Step 1: Build the object map
List the main objects in the app:
- user
- org/tenant/team
- project
- report/export
- admin tools
- payments/billing
Step 2: Build an access matrix
Create two users:
- User A (normal)
- User B (normal)
(Optional: admin/moderator if it exists)
Then test:
- Can A read B’s objects?
- Can A update B’s objects?
- Can A call admin functions?
Step 3: Mine IDs aggressively
Where to pull IDs:
- list endpoints
- UI URLs
- network tab
- exports
- notifications
- GraphQL responses (IDs everywhere)
Step 4: Fuzz and diff
Don’t just look for “200 vs 403.”
Look for subtle changes:
- small field differences
- partial objects returned
- count differences
- timing differences
Step 5: Validate impact
A real report should show:
- exact request(s)
- what changed
- what data was exposed or action performed
- why it’s unauthorized
Fixing authorization issues (what developers should actually do)
If you build APIs, the fix patterns are consistent:
Fix BOLA/IDOR
- Enforce ownership checks in the data layer:
WHERE id = ? AND owner_id = ?
- Prefer deny-by-default policies
- Add authorization tests for every sensitive route
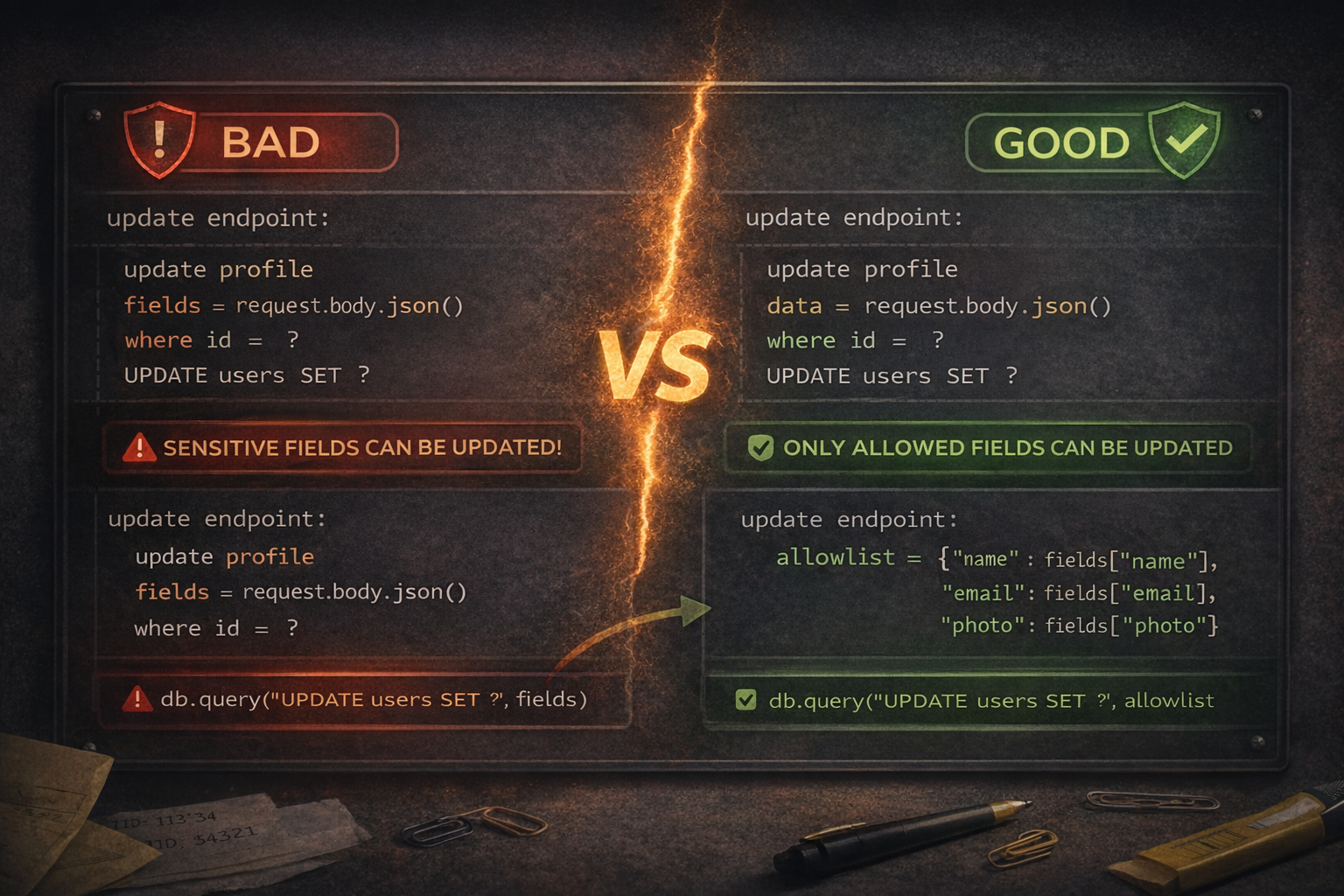
Fix BOPLA/Mass Assignment
- Use allow lists for update endpoints
- Reject unknown fields
- Separate “user-editable” fields from “system” fields
Fix BFLA
- Centralize role checks (middleware/policy engine)
- Don’t rely on “admin UI only”
- Log and alert on access-denied attempts for privileged routes
Practice targets (hands-on)
If you want to learn these the fastest way: practice on realistic, multi-step labs.
On WebVerse Labs, the writeups and labs are designed around the same authorization failure patterns you see in real APIs:
- Mass assignment / role escalation (BOPLA)
- Export/download BOLA/IDOR
- Admin function exposure patterns and chaining
Wrap-Up: How API Authorization Failures Actually Happen in Real Apps
The biggest mistake people make when learning API security is treating authorization bugs like “weird edge cases.”
They’re not.
They’re some of the most common, high-impact, and repeatedly exploitable vulnerabilities in modern web apps — especially in systems built from multiple APIs, dashboards, subdomains, and internal tools.
And the reason they’re so dangerous is simple:
- the requests often look completely normal
- the backend is usually “working as designed”
- the bug is in the authorization logic, not the syntax or framework
That’s why these issues survive code review so often.
The core idea to remember: Object, Property, Function
If you remember nothing else from this post, remember this model:
- Object-level (BOLA / IDOR): Can I access a record I don’t own?
- Property-level (BOPLA / Mass Assignment / Excessive Data Exposure): Can I read or modify fields I shouldn’t?
- Function-level (BFLA): Can I call actions my role should not be allowed to execute?
That framework makes API testing faster because it gives you a repeatable way to think:
- What object is this?
- What fields are exposed or writable?
- What function is this endpoint performing?
- Who is supposed to be allowed to do this?
Why these bugs chain so well
In real-world assessments, authorization failures rarely stay isolated.
A small bug like:
- reading another user’s export (BOLA)
- changing a privileged field (mass assignment / BOPLA)
- calling a hidden admin function (BFLA)
can immediately become a pivot into:
- account takeover
- privilege escalation
- internal API access
- sensitive config exposure
- full tenant data exposure
That’s why good API testing is not just “send one modified request and stop.” It’s:
- test the first flaw
- map what it unlocks
- enumerate what changed
- validate impact end-to-end
For testers: focus on behavior, not labels
The labels matter for reporting and learning, but during testing, the highest-signal mindset is:
- What should this request do?
- What does it actually do?
- Who should be allowed to perform it?
- What data should be hidden or immutable?
If you keep that mindset, you’ll find authorization bugs much faster than if you only hunt for one category at a time.
For developers: the fix is consistency, not patching one endpoint
The real fix for API authorization failures is not “tighten one route.”
It’s building systems that are authorization-first:
- deny by default
- enforce object ownership in the query/policy layer
- allowlist writable fields
- minimize returned fields
- centralize role/permission checks
- test authorization paths just like business logic
A secure UI is nice. A secure backend is mandatory.
Final takeaway
API authorization failures are not “advanced tricks” — they are fundamental web/API security issues that appear in normal apps, normal code, and normal workflows.
If you can reliably test objects, properties, and functions, you’ll catch a huge percentage of real-world API bugs.
If you want hands-on practice with these patterns (BOLA/IDOR, mass assignment/BOPLA, and function-level authorization failures), you can practice realistic labs and walkthroughs on webverselabs.com.
FAQ: API Authorization Failures (BOLA, BOPLA, BFLA, IDOR, and Broken Access Control)
What is an API authorization failure?
An API authorization failure happens when the backend does not properly verify whether the current user is allowed to access a resource, modify a field, or perform an action.
In practice, this often looks like a normal API request that should be rejected (403/401) but is incorrectly allowed.
What is the difference between authentication and authorization in APIs?
- Authentication answers: Who are you? (session, JWT, API key, OAuth token)
- Authorization answers: What are you allowed to do? (which objects, fields, and functions you can access)
A user can be fully authenticated and still exploit an authorization bug if the API trusts them too much.
What is BOLA in API security?
BOLA stands for Broken Object Level Authorization.
It happens when an API uses an object ID (such as a numeric ID, UUID, slug, or tenant ID) but fails to verify that the authenticated user is allowed to access that object.
Example:
A user requests /api/orders/1234 and receives another user’s order.
Is BOLA the same as IDOR?
They are closely related and often used interchangeably in practice.
- IDOR (Insecure Direct Object Reference) is the older/common term
- BOLA (Broken Object Level Authorization) is the OWASP API Security term
Both describe object-access bugs where changing identifiers leads to unauthorized access.
Do UUIDs prevent IDOR/BOLA vulnerabilities?
No.
UUIDs can make identifiers harder to guess, but they do not replace authorization checks. If an attacker gets a UUID through logs, shared links, exports, API responses, or UI leaks, the API must still enforce ownership and access control.
UUIDs reduce guessing risk. They do not solve broken authorization.
What is BOPLA in API security?
BOPLA stands for Broken Object Property Level Authorization.
It happens when an API lets users read or modify object properties they should not control or see.
This includes:
- mass assignment (write) issues
- excessive data exposure (read) issues
What is mass assignment in an API?
Mass assignment happens when the server accepts client-supplied JSON too broadly and updates backend model fields without strict allowlisting.
Example:
A profile update endpoint meant for name and email also accepts role, isAdmin, or permissions, allowing privilege escalation.
What is excessive data exposure in an API?
Excessive data exposure is when an API returns fields that the current user should not see, even if they cannot modify them.
Examples include:
- internal notes
- reset tokens or reset codes
- permission structures
- staff-only metadata
- debug fields
- internal IDs or service info
What is BFLA in API security?
BFLA stands for Broken Function Level Authorization.
It occurs when an API exposes privileged actions (admin/moderator/staff functions) but fails to enforce role/permission checks on the backend.
Example:
A normal user can access /api/admin/exportUsers or /api/mod/audit because the endpoint exists and lacks proper authorization checks.
What is the difference between BOLA, BOPLA, and BFLA?
Think of it as three authorization layers:
- BOLA / IDOR (Object): Can I access this object?
- BOPLA (Property): Can I read or change this field?
- BFLA (Function): Can I execute this action?
This model is one of the fastest ways to structure API authorization testing.
Why are API authorization bugs so common?
They are common because modern apps are made of many APIs and services, and authorization logic is often:
- duplicated
- inconsistently implemented
- tied too closely to frontend behavior
- missing on “secondary” endpoints
- difficult to validate without real multi-user tests
Authorization bugs are logic flaws, not syntax errors, so code can appear correct while still being insecure.
What are the most common places to find BOLA/IDOR bugs?
High-signal BOLA/IDOR hotspots include:
- export/download endpoints (PDFs, ZIPs, reports, receipts)
- invoices/orders/tickets/cases/projects
- endpoints with
?id=or/resource/{id} - multi-tenant routes with
orgId,teamId,tenantId - “view details” endpoints
- internal API routes exposed through frontend network calls
How do you test BOLA/IDOR quickly?
A high-signal workflow is:
- Create two users (A and B)
- Browse normally and collect object IDs
- Replay A’s request with B’s object ID
- Diff responses (not just status codes)
- Validate whether unauthorized data or actions are possible
The most important step is response diffing — many auth bugs don’t show up as a clean 200 vs 403 difference.
How do you test mass assignment (BOPLA write) in APIs?
Start with a normal update request (profile/settings/account) and add high-signal fields like:
roleisAdminpermissionsplansubscriptionemailVerifiedmfaEnabledorgId/userId(if present)
Then replay and check:
- response changes
- role/permission changes
- new access to privileged routes
- session/JWT behavior (you may need to re-login)
How do you test excessive data exposure (BOPLA read)?
Look at API responses and ask:
- Does the frontend actually need every returned field?
- Are there internal/debug/staff-only properties in the response?
- Do two different users receive different hidden metadata?
- Are full models being serialized instead of filtered DTOs?
A strong tactic is comparing the same endpoint response across different users/roles.
How do you test BFLA (Broken Function Level Authorization)?
Identify likely privileged endpoints and functions, then test them as a lower-privileged user.
High-signal paths/keywords include:
/api/admin/*/api/mod/*/api/internal/*exportauditconfigresetgrant-roledownload-all
Try direct requests, replay requests, and observe whether the server truly enforces role checks.
Why is the UI not a security boundary?
Because attackers do not need to use the UI as intended.
They can:
- intercept requests
- modify JSON bodies
- replay hidden endpoints
- call APIs directly with curl/Burp/Postman
- fuzz endpoints the UI never links to
If the backend relies on “the button is hidden” instead of real authorization checks, the API is vulnerable.
What does a good API authorization bug report include?
A strong report should include:
- exact endpoint(s)
- exact request(s)
- exact unauthorized behavior
- affected roles/objects/fields/functions
- proof of impact (data exposed, action performed)
- expected vs actual behavior
- remediation guidance (ownership checks, allowlists, role enforcement)
This makes the issue actionable for developers and easier to triage.
How should developers fix BOLA/IDOR vulnerabilities?
Developers should enforce ownership and access checks server-side for every object request.
Common fix patterns:
- query by object + owner/tenant (
WHERE id=? AND owner_id=?) - deny by default
- centralized policy enforcement
- tenant scoping in every data access path
- authorization tests for all sensitive routes
How should developers fix mass assignment and BOPLA issues?
Fix patterns include:
- strict server-side allowlists for writable fields
- rejecting unknown fields
- separate DTOs/schemas for user-editable data
- never trusting client-supplied privilege fields
- minimizing response fields to only what the frontend needs
How should developers fix BFLA vulnerabilities?
Fix patterns include:
- centralized role/permission middleware or policy checks
- function-level authorization on every privileged route
- deny-by-default admin/internal endpoints
- auditing and logging failed privileged access attempts
- avoiding “hidden UI button = protected function” assumptions
What is the best way to practice API authorization testing?
The fastest way to improve is hands-on practice with realistic labs that include:
- multiple users/roles
- object IDs
- writable JSON bodies
- admin-only functions
- chained exploitation paths
You can practice these patterns (BOLA/IDOR, BOPLA/mass assignment, BFLA, and API exploit chaining) on webverselabs.com.